Ledger Live Login — A Complete Beginner-Friendly Guide to Secure Crypto Access
Learn how to log in safely, understand why hardware wallets stay secure, avoid phishing, and manage your crypto ecosystem using Ledger Live with confidence and clarity.
Why Logging Into Ledger Live Requires Care
Cryptocurrency empowers users by placing control directly in their hands — but this responsibility means that security becomes extremely important.
Ledger devices protect private keys offline using cold storage and secure elements, but the login process still must be handled correctly.
Fake applications, look-alike websites, and phishing pages often target users searching for “Ledger Live login.”
**Understanding the correct workflow helps you avoid these traps while maintaining full control of your assets.**
Ledger devices protect private keys offline using cold storage and secure elements, but the login process still must be handled correctly.
Fake applications, look-alike websites, and phishing pages often target users searching for “Ledger Live login.”
**Understanding the correct workflow helps you avoid these traps while maintaining full control of your assets.**
What Ledger Live Really Does
Ledger Live acts as the interface between you and your hardware wallet.
Signing transactions happens only on the physical device, making remote compromise nearly impossible.
- Track portfolio values
- Send/receive transactions
- Update firmware
- Connect to decentralized apps
- Manage multiple blockchains
Signing transactions happens only on the physical device, making remote compromise nearly impossible.
A Story of Almost Losing Everything
Daniel purchased a Ledger Nano S and googled “Ledger Live login.”
A clean, modern page appeared and requested that he “confirm backup words.”
Luckily, Daniel remembered reading that **ledger devices never ask for recovery phrases online**.
He closed the page, checked the official domain, and avoided a major loss.
**Scammers rely on urgency and trust — knowing the correct process breaks their strategy.**
A clean, modern page appeared and requested that he “confirm backup words.”
Luckily, Daniel remembered reading that **ledger devices never ask for recovery phrases online**.
He closed the page, checked the official domain, and avoided a major loss.
**Scammers rely on urgency and trust — knowing the correct process breaks their strategy.**
Ledger Live Login — Step-by-Step
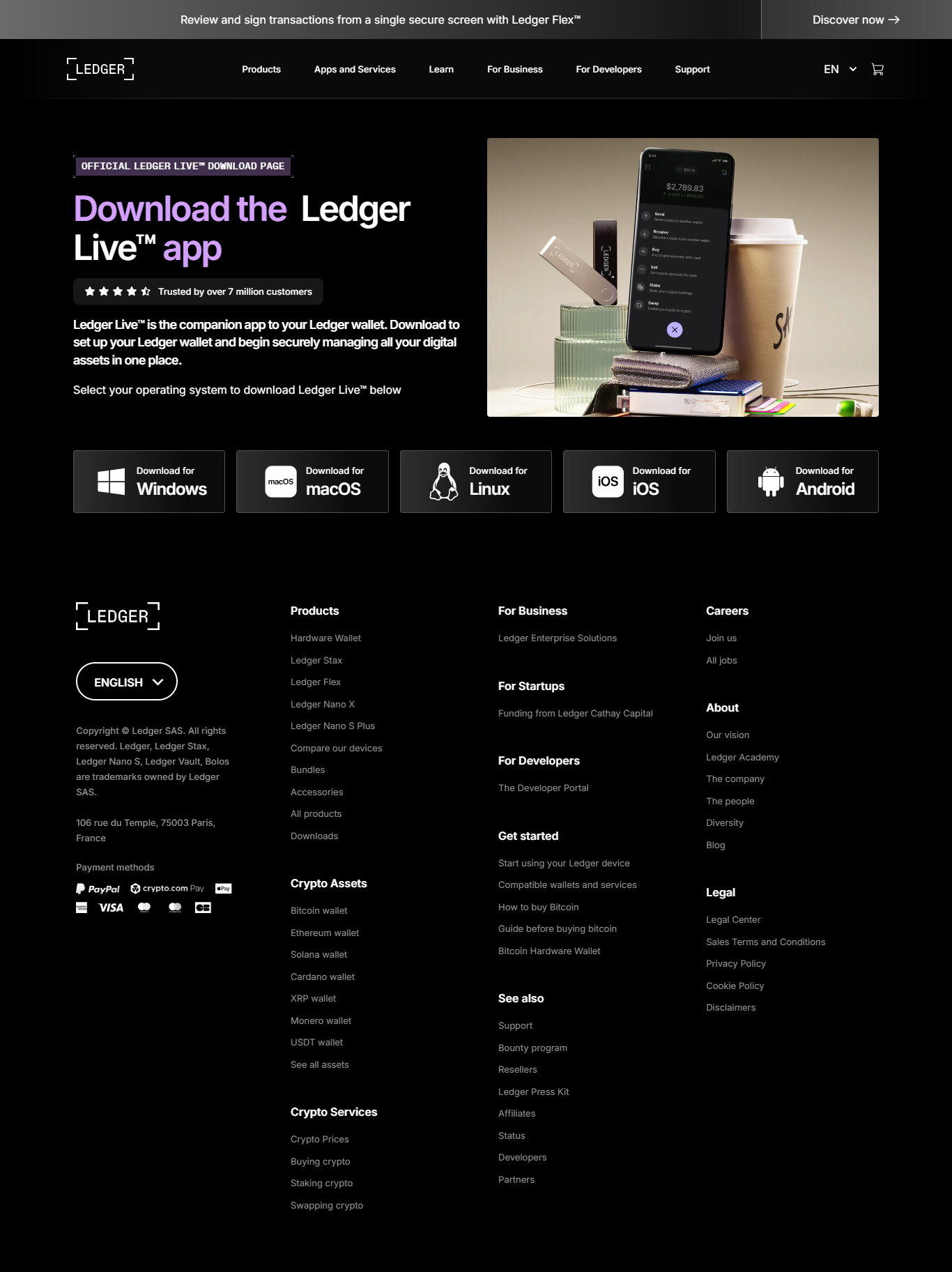
1. Download Only From Ledger.com
Never trust search engine results or sponsored links.
2. Install and Open Ledger Live
Available on Windows, macOS, Linux, and mobile.
3. Connect Your Ledger Device
Use USB or Bluetooth depending on the model.
4. Enter PIN on the Device Only
Your computer never sees your PIN — authentication remains offline.
How Ledger Keeps Keys Secure
Ledger relies on:
- Secure Element chips
- Offline transaction signing
- Protected recovery phrase handling
- Physical verification screen
Wallet Comparison Overview
| Wallet Type | Security Level | Key Control | Best Use |
|---|---|---|---|
| Ledger Hardware Wallet | Very High | User | Cold storage |
| Hot Wallet | Medium | User | Everyday use |
| Exchange Wallet | Low | Exchange | Trading |
Key Security Reminders
✔ Always download official software
✔ Never type your recovery phrase online
✔ Keep backups offline
✔ Verify transactions on the device screen
✔ Beware of clones and fake support pages
✔ Keep firmware updated
✔ Never type your recovery phrase online
✔ Keep backups offline
✔ Verify transactions on the device screen
✔ Beware of clones and fake support pages
✔ Keep firmware updated
Frequently Asked Questions
1. Does Ledger Live store private keys?
No — keys remain inside the hardware device.
2. Does it require a password?
No — the PIN is entered only on the device.
3. Can it be hacked?
Not in a way that exposes keys, because signing is offline.
4. Does it support many coins?
Yes — thousands across multiple chains.
5. What if the device is lost?
Restore your wallet using the recovery phrase on a new device.
No — keys remain inside the hardware device.
2. Does it require a password?
No — the PIN is entered only on the device.
3. Can it be hacked?
Not in a way that exposes keys, because signing is offline.
4. Does it support many coins?
Yes — thousands across multiple chains.
5. What if the device is lost?
Restore your wallet using the recovery phrase on a new device.
Conclusion — Authentic Login Keeps You Safe
Ledger Live is a powerful tool, but its safety relies on correct usage and understanding of the underlying architecture.
By using only official software, avoiding imitation pages, and trusting the physical device rather than online prompts, you create a secure environment for your crypto assets.
Ledger’s combination of cold storage, secure elements, and offline signing sets a high security standard — but users must still follow safe login practices.
Always choose the official path — your crypto’s safety depends on it.
By using only official software, avoiding imitation pages, and trusting the physical device rather than online prompts, you create a secure environment for your crypto assets.
Ledger’s combination of cold storage, secure elements, and offline signing sets a high security standard — but users must still follow safe login practices.
Always choose the official path — your crypto’s safety depends on it.